               |
               |
This on-site couse can also be conducted for customers in Lahore, and Islamabad
Zero Trust has become an extremely popular reference for security best practices. Vendor marketing and other misleading data has unfortunately caused confusion about what Zero Trust is and how to use it properly. This misunderstanding of Zero Trust can lead to a false sense of security. This course will review the history of many popular terms for security best practices as well as how the industry developed the term Zero Trust. We will review Zero Trust Architecture and Framework in details with enterprise use cases. Topics will include network, endpoint and cloud security concepts. We will also discuss misconceptions, such as how Zero Trust best practices can t be achieved by simply acquiring a technology such as a Firewall, Identity Management solution or Network Access Control offering. Expect many real-world examples, demos and definitions of topics that you can relate to as well as evaluate with open source or enterprise technology. The training course flow will be a mix of lectures & classroom discussions so that participants can have a detailed understanding of various components of cybersecurity technologies. ABOUT
THE INSTRUCTOR Our instructor holds various
industry professional certifications in the space
of enterprise servers and storage technologies,
Information Security, Enterprise Architecture,
Blockchain, ITIL, Cloud, Virtualization, Green IT,
and a co-author of 10 IBM Redbooks and have
designed and developed 70 plus courses based on
storage, information security, cybersecurity,
enterprise architecture, Blockchain, Open Banking
Framework and digital technologies stacks.
TARGETED
AUDIENCE:
Participants attending this workshop should be familiar with basic Information Technology (IT) and Security concepts, business challenges and the role of general system wide infrastructure technologies and their applications. COURSE OUTLINE
      |
|
|
|
|

FINCA
Microfinance Bank Ltd, Central Depository Company,
and Consulting |

Habib
Bank Ltd, Dubai Islamic Bank, Emirates NBD Bank,
EETS, and |

State
Bank of Pakistan and Consulting Business Services
has attended |

Dubai
Port World, Institute of Business Administration
(IBA), Kyndryl Canada, |

State
Bank of Pakistan, National Bank of Pakistan, Habib
Bank Limited, |

The Bank
of Punjab, NRSP Microfinance Bank Ltd, GBM
Pakistan, |
Securities
and Exchange Commission of Pakistan (SECP) and
GBM |

Habib
Bank Limited has attended a two-day Face-to-Face
workshop on |
 National Bank of Pakistan has attended a
two-day Face-to-Face workshop on
|
|
United
Bank Limited has attended
a two-day Face-to-Face Client onsite |
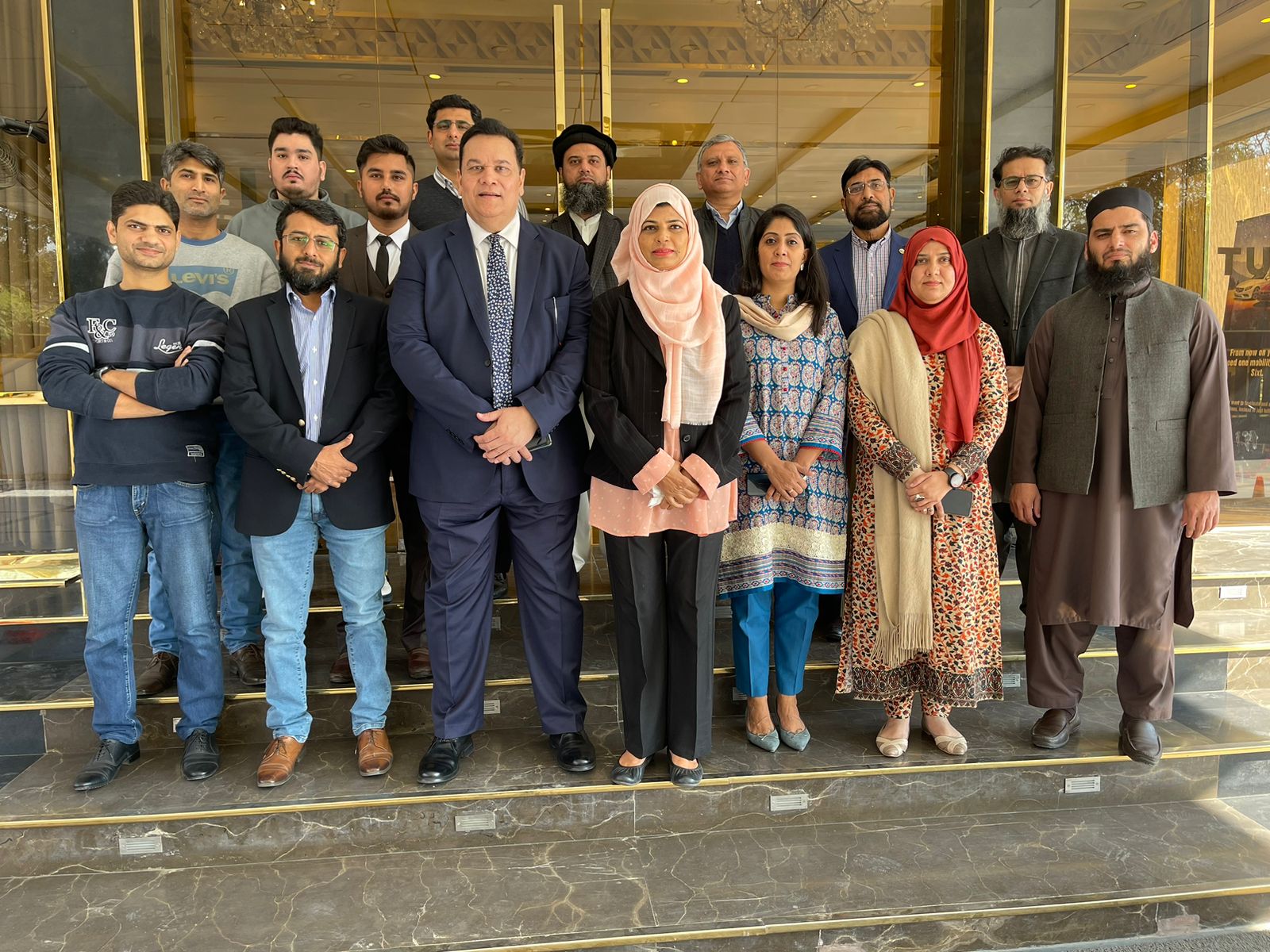
National Bank of Pakistan has attended a two-day Face-to-Face workshop on "Zero Trust Security Architecture Framework" imparted by Adnan Ikram on November 18 & 19, 2024 at Marriott Hotel in Karachi. |
|
      
|