| Course
Title |
: Zero
Trust Security Implementation for the Hybrid
Enterprise |
| Course
Duration |
: 2 Day
Face-to-Face Classroom and 2 Day Online
Instructor Led Workshop
: Online
workshop is delivered in two days, two units
each day between 9:15 am to 1 pm and 2:30 pm
to 5:30 pm |
| Course Fee |
: Available
upon request (Write to us at info@tlcpak.com) |
| Course
Location |
: TLC
Office, Customer Onsite, and Online |
| Course Code |
: TN324 |
| Deliverables |
:
Comprehensive Student Guide and Workshop
Certificate |
This on-site
course can also be conducted for customers in
Lahore, and Islamabad
PURPOSE:
In a
nut-shell, the concept of a Zero Trust
Security Architecture has been around for
more than a decade, but adoption did not
really begin to take hold until the past
couple of years. Zero Trust is a framework
for securing organizations in the cloud,
on-premises and mobile world that asserts
that no user or application should be
trusted by default. Following a key zero
trust principle, least-privileged access,
trust is established based on context (e.g.,
user identity and location, the security
posture of the endpoint, the app or service
being requested) with policy checks at each
step.
Zero
Trust Architecture is an alternative
security model that addresses the
fundamental flaw of traditional strategies
that data only needs to be protected from
outside of an organization. The Zero Trust
model views data security through a new
lens, enabling parameters that dictate
access and restrictions.
Understand
how segmentation gateway provides granular
visibility into traffic and enforces
additional layers of inspection and access
control with granular Layer 7 policy based
on the Kipling Method.
Zero
Trust is an augmentation of your existing
architecture, it does not require a
complete technology overhaul. Rather, it
can be deployed iteratively while allowing
you to take advantage of the tools and
technologies you already have.
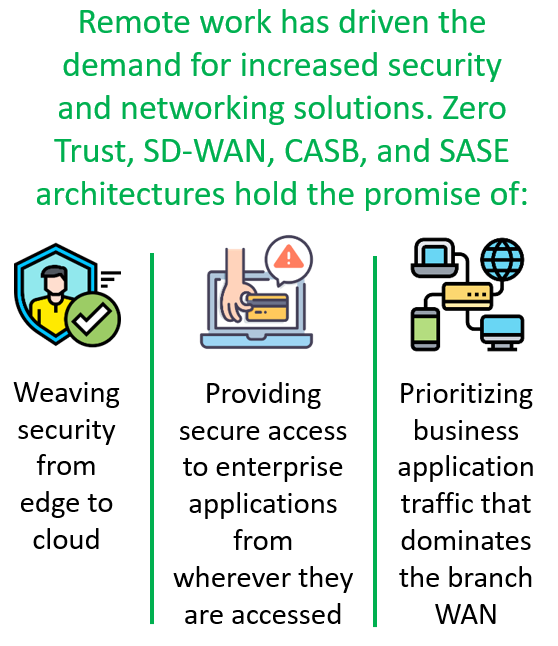
When
organizations shifted toward accelerated
digital transformation to the cloud, the
VPN became a bottleneck that was
impossible to scale. This is where the
need for having a Software Defined
Parameter (SDP) arises.
In this
massive shift to cloud applications and
digital transformation, Cloud Access
Security Brokers emerged. CASBs aim to
mitigate risks around cloud assets when
users access those assets from inside the
organization's perimeter.
CHOOSING
BETWEEN CASB AND SASE ARCHITECTURES
CASB vs.
SASE both offer benefits to enterprises
depending on the situation and
conditions.
A CASB
solution can be deployed as a standalone
framework that easily integrates into an
enterprise’s existing security
architecture.
However,
SASE is increasingly seen as the preferred
option as it builds on CASB capabilities
while simplifying security and maximizing
the efficiency of a company’s IT and
security architecture under an Hybrid
Model.
The training course flow will
be a mix of lectures & classroom
discussions so that participants can
have a detailed understanding of various
components of cybersecurity
technologies.
|
|
 |
ABOUT THE
INSTRUCTOR
This workshop shall
be delivered by TOGAF 9 Certified/IBM Certified
Infrastructure System Architect and an experienced
trainer with 25+ years of career experience
imparting education and training services both
locally and internationally and have worked for
international enterprise technology vendors
including IBM, Fujitsu, and ICL. Our instructor
holds various industry professional certifications
in the space of enterprise servers and storage
technologies, Information Security, Enterprise
Architecture, ITIL, Cloud, Virtualization, Green IT,
and a co-author of 10 IBM Redbooks.
TLC has
successfully delivered this workshop six times in
the recent past with 100% client satisfaction
feedback.
TARGETED
AUDIENCE:
This workshop is intended for resources
who/from:
- CIO, CTO, CISO, CDO, Business and
Digital Leaders, IT Director and IT Managers,
Application/Database teams, Audit, Risk and
Compliance, Information Security and
Cybersecurity Professionals, IT Operations,
Project Managers, Enterprise Architects, Network
Operation Teams, and Technical Writers with a
familiarity of basic IT/IS concepts who want to;
- Want to learn new trends in security
and data breach incidents.
- Interested in entering the field of
Information Security and Cybersecurity.
- Students and fresh graduates.
- Managers, Senior IT Managers, Business
and HR Leaders who want to refresh their present
knowledge.
- Security Operations Center teams.
- Network Operations Centers.
Workshop
Summary
- Understand
the true meaning of the Zero Trust security
framework
- Determine how
to apply security best practices represented in
the latest Zero Trust framework to your
organization.
- Understand
how to assess your existing security capabilities
and map out a plan for improving your
organization’s security practice.
- Understand
security best practices for all areas of your
business (cloud, endpoint and network).
- Understand
why CASB and SASE Architecture are important for
implementing Zero Trust in the Hybrid Enterprise
using Public and Private cloud services.
- Unleash the
importance for having a Software Defined WAN in
the Hybrid Enterprise environment and a comparison
between MPLS and SD-WAN technologies.
PREREQUISITES:
Participants
attending this workshop should be familiar with basic
Information Technology (IT) and Security concepts,
business challenges and the role of general system
wide infrastructure technologies and their
applications.
This course is
recommended for customers who have earlier attended
TLC course on "Zero Trust
Security Architecture Framework" Course Code:
TN224. For additional information on this course
click on the course link.
COURSE
OUTLINE
Unit 1 – Zero Trust
Security Architecture Framework
- Things
that you cannot ignore – Cyber Crime
Statistics.
- What
do your device know about you – An eye
opener discussion.
- Assess
and mitigate vulnerabilities in mobile
systems.
- How
an Advanced Persistent Threats attack
works.
- Zero
Trust common IT challenges.
- Understanding
Zero Trust Architecture.
- Describe
Segmentation Gateway – An essential
component of Zero Trust.
- Zero
Trust: As Dynamic as Your Enterprise.
- Deploying
Zero Trust.
- How
to achieve a Zero Trust Architecture
Model?
- Zero
Trust scenarios, Zero Trust scope and
phases.
- Zero
Trust architecture services – An
Example.
- Identity
Governance and Administration Strategy.
- Implementing
Zero Trust Identity Management
Principles.
- Zero
Trust Implementation Methodology.
- Understanding
the Zero Trust Model.
- How
do you approach Zero Trust governance?
- Key
steps to Risk Management for Zero Trust.
- Recommendations
for starting a Zero Trust Journey.
- Digital
Enterprise based on Zero Trust adoption
– A Bigger View.
- Zero
Trust Architectural Framework.
- Zero
Trust Maturity Levels.
- What
are the threats to Zero Trust
Architecture?
- Zero
Trust Best Practices.
- VPN
Vs Zero Trust networks.
- Difference
between SDP, VPN and Zero-Trust
Networks.
- Principles
of Zero Trust applied to IoT.
- Top
Zero Trust Solutions.
- Test
your response plan to prepare for
cyberattack.
- Unit
1 Assessment
Unit
2 – User and Entity Behavior Analytics
Fundamental Principles
- UEBA
– User and Entity Behavior Analytics
Defined.
- Why
do organizations need UEBA?
- How
UEBA works with SIEM.
- UEBA
integration with SIEM.
- Similarities
and Dissimilarities between SIEM and
UEBA solution.
- Facts
for a successful implementation of UEBA
solution.
- How
User and Entity Behavior Analytics work?
- Exploring
main components of UEBA.
- Understand
essential pillars of UEBA.
- UEBA
Risk Scoring and Threat Indicator Signs.
- User
and Entity Behavior Analytics for
Enterprise Security for threat hunting
and incident investigation.
- Critical
Components of UEBA Systems.
- Seven
Best Practices for building a baseline
of User Behavior.
- Define
Use case - Define Data Source, Define
Behaviors, Establish the Baseline,
Update Policies and Training wareness
Program, Conduct Testing, Rebuild
Baseline.
- Some
of the Disadvantages of using UEBA
solution one should know.
- Key
specifications for selecting a good UEBA
solution.
- Unit
2 Assessment.
|
Unit 3 – The Role of
CASB and SASE in Implementing Zero Trust
Security
- Understand
Zero-day Attack.
- Cloud
Management Components and Cloud
Architecture.
- Cloud
Computing Reference Architecture – CCRA.
- NIST
Cloud Computing Reference Architecture.
- The
Top 7 Advanced Cloud Security
Challenges.
- The
6 Pillars of Robust Cloud Security.
- Top
Cloud Application Security Threats.
- Cloud
security features required for Cloud
Computing Models.
- Understand
Cloud Access Security Broker.
- Security
features offered by Cloud Access
Security Broker.
- How
Cloud Access Security Broker work.
- Requirements
of a CASB Solution.
- Why
do I need a CASB solution?
- Cloud
Access Security Broker Solution
Deployment Models.
- Three
key considerations for choosing a CASB.
- Multi-Mode
Next-Gen CASB Architecture.
- Use
cases for Cloud Access Security
Broker.
- Use
cases for Cloud Access Security
Broker.
- Gartner’s
10 Best Practices for Successful CASB
Projects.
- Cloud
Access Security Broker Vs. Secure Access
Service Edge.
- CASB
and SASE – Pros and Cons.
- Privileged
Access Management Defined.
- Unprivileged
to Privileged Access Management using
Zero Trust Architecture.
- Digital
Enterprise based on Zero Trust
Architecture – A Bigger View.
- Cloud
Security Best Practices any Organization
should follow.
- Understand
Secure Access Service Edge (SASE).
- SASE
Architecture – CASB within SASE.
- Pros
and Cons of SASE & CASB– Advantages
and challenges for enterprises.
- Comparative
Analysis on SASE Vs. CASB.
- Unit
3 Assessment.
Unit 4 – Exploiting
Software- Defined WAN
- Business
Challenges that develop the need for
considering an SD-WAN.
- What
business problems does SD-WAN solve?
- Software-defined
Wide Area Network (SD-WAN) Defined.
- Planning
for your SD-WAN solution.
- SD-WAN
Key Characteristics.
- Zero-Touch
Provisioning – An impressive capability
of SD-WAN.
- Main
components that make up the basic
structure of an SD-WAN.
- Main
types of SD-WAN Architectures.
- MPLS
defined and difference between SD-WAN
and MPLS.
- MPLS
Vs SD-WAN – Pros and Cons.
- SD-WAN
Architecture – Flexibility and
Scalability.
- How
does SD-WAN work?
- Build
an effective SD-WAN security strategy at
the branch.
- Three
Models for an SD-WAN Deployment.
- Evaluate
where to deploy the SD-WAN controller.
- Assess
connectivity choices for SD-WAN
deployment.
- SD-WAN
Policy Types.
- SD-WAN
and MPLS – Differentiating between the
two technologies.
- Describe
SD-WAN Orchestration – Orchestration Vs.
Cloud Automation.
- Other
benefits of SD-WAN – Highlights.
- SD-WAN
Use-cases.
- SD-WAN
Checkpoints.
- Unit
4 Assessment.
|
|
|

|